Google Cloud Storage (GCS)
Steps to add a Google Cloud Storage Bucket as a data destination
Setup Instructions
Steps to add a Google Cloud Storage Bucket as a data destination.
Step 1: Create a service account
- In the GCP console, navigate to the IAM & Admin menu.
- Click into the Service Accounts tab.
- Click Create service account at the top of the menu.
- In the first step, name the service account that will be used to transfer data into Cloud Storage and click Create and Continue. You may continue through the following steps without assigning any roles, and in the final step, click Done.
Step 2: Create destination GCS bucket
- Navigate to the Cloud Storage page.
- Click Create.
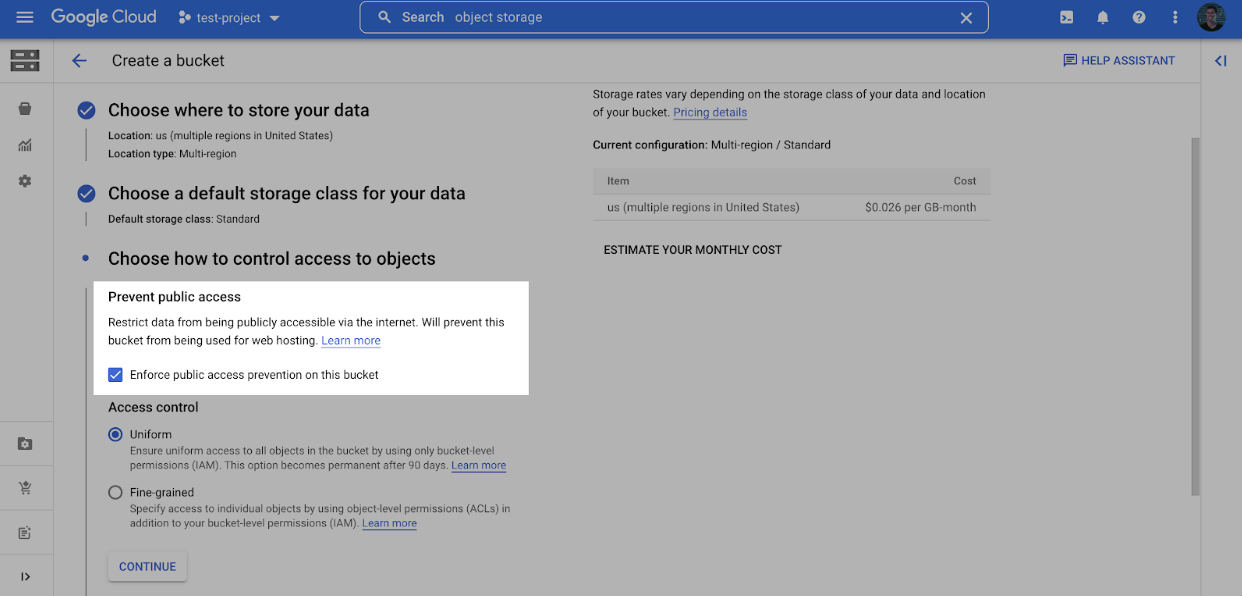
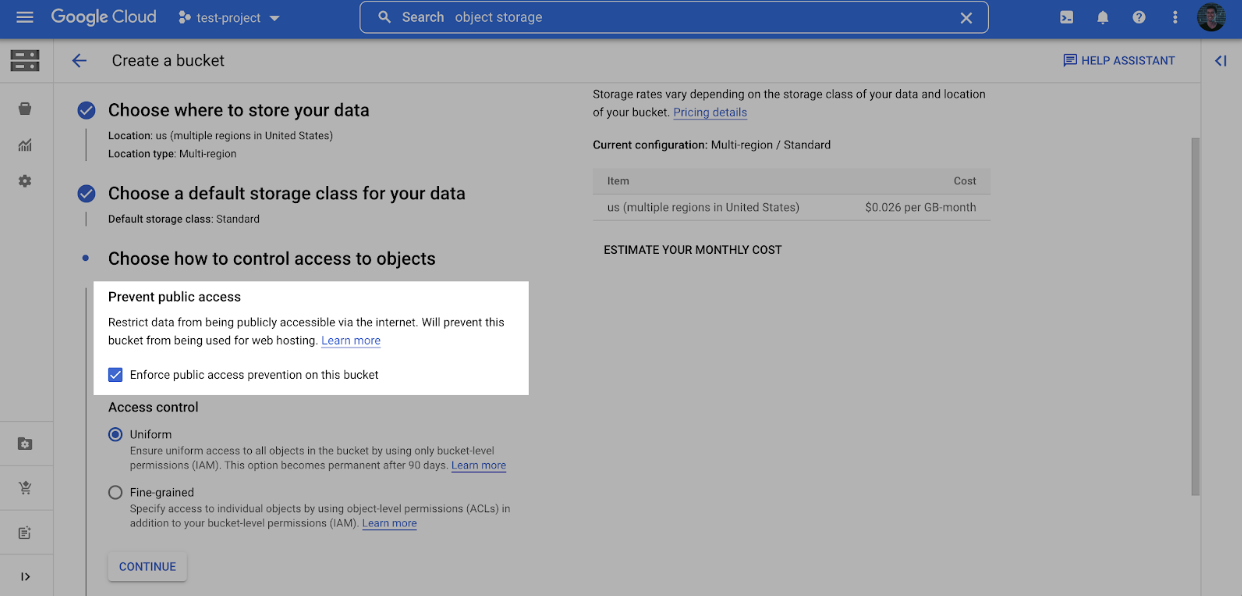
- Enter a bucket name, choose a region. Note: at the Choose how to control access to objects step, we recommend selecting Enforce public access prevention on this bucket.
- After selecting your preferences for the remaining steps, click Create.
- On the Bucket details page for the bucket you created, select the Permissions tab, and click Grant access.
- Grant access to the principal (Service Account) you created in Step 1, and assign the Role: Storage Object Creator. Click Save.
Step 3: Generate HMAC key
An HMAC key is a type of credential and can be associated with a service account or a user account to access Google Cloud Storage.
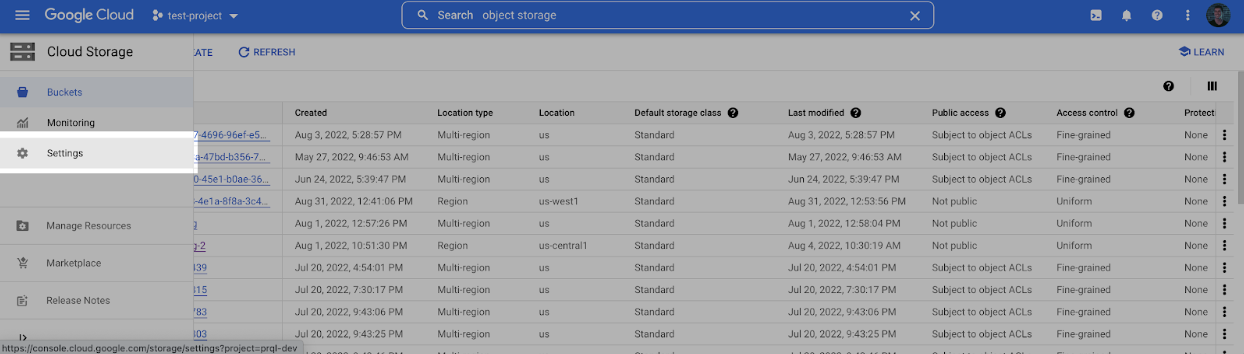
- Navigate to the Cloud Storage page.
- Click into the Settings tab on the left side menu.
- Make a note of the Storage URI (usually https://storage.googleapis.com) and then click the Create a key for a Service Account button.
- Select the Service Account created in Step 1, and click Create key.
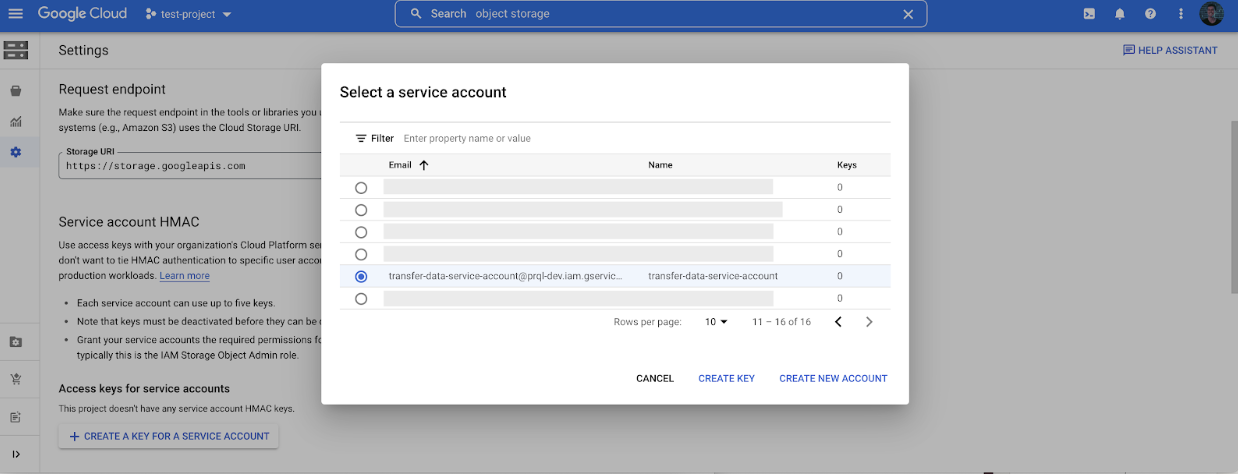
- Make a note of the Access key and Secret.
Step 4: Connect your GCS Bucket to Fairing!
Share the Bucket name and Storage URI with Fairing, and then use the form provided by Fairing to connect your GCS Bucket.
Note: your Google Cloud Storage Bucket will be entered under the S3 option, with the following considerations:
- Port: 443
- AWS Access Key ID: your HMAC Access Key generated in Step 4.
- AWS Secret Access Key: your HMAC Secret generated in Step 4.
Updated about 1 month ago